- 1) Introduction
- 2) Understanding Biometric Technology
- 3) Types of Biometric Authentication Technologies
- 4) The Benefits of Biometric Access Control
- 5) Implementing Biometric Access Control Systems
- 6) Transforming Workplace Security with Biometrics
- 7) The Evolution Roadmap for Biometric Access Control
- 8) Factors to Consider Before Adopting Biometrics
- 9) Conclusion
- 10) FAQs
Introduction
Physical access control is a crucial part of an organization’s security strategy. It regulates who can enter sensitive areas like offices, data centers, and restricted zones. Access control systems traditionally rely on keys, pin codes, ID cards, and guards. However, these legacy mechanisms have several vulnerabilities that malicious actors can exploit.
This has led to the growing adoption of biometric access control systems that use human characteristics for authentication. Biometrics verify identity by analyzing unique biological traits. This results in robust, foolproof access control that is also highly convenient for authorized staff.
In this comprehensive guide, we dive deep into biometric technology and how it is transforming workplace access control:
- Core concepts like how biometrics work
- An overview of popular biometric modalities
- Benefits of biometric access control systems
- Implementation best practices
- Transforming workplace security with biometrics
- The future evolution of biometric technology
- Factors to consider before adoption
Let’s get started.
Understanding Biometric Technology

Before looking at biometric access control systems, it is useful to understand the core principles of biometric authentication.
What are Biometrics?
Biometrics refers to identification and authentication techniques that rely on measurements of human characteristics. In access control systems, biometrics verify a person’s identity before granting entry into restricted areas.
There are two main categories of biometric traits:
Physical biometrics – Analyze static physical attributes like fingerprints, faces, irises, retina, ears, palms, DNA, and hand measurements. Physical traits are unique for each individual.
Behavioral biometrics – Focus on patterns in human activities and traits like voice, signature, gait, keystroke dynamics, and lip movements. Behavioral attributes may not be entirely unique but provide secondary authentication.
Biometric authentication works by comparing an individual’s freshly captured biometric data against previously stored reference templates to determine a match. If there is a sufficient match, the identity is confirmed and access is granted.
The Biometric Authentication Process
Let’s look at the step-by-step process:
1. Capture – The user’s biometric data is captured using an electronic sensor. For example, a fingerprint scanner captures the digital image of a person’s finger placed on the reader.
2. Extraction – Key biometric features are extracted from the raw data to create a compact digital representation or template. For fingerprints, minutiae points and ridge patterns may be removed.
3. Enrollment – The initial biometric template is securely stored in a database for later comparison. This enrolled template functions as the user’s unique digital identity.
4. Authentication – When the user needs access, their live biometric data is captured again. The new template is compared against enrolled templates to find a match.
5. Matching – Advanced matching algorithms consider various parameters to determine if the captured and enrolled templates are similar enough to confirm a match. If yes, access is allowed.
To account for natural variations, biometric systems do not require an exact match. They allow for slight changes in the data while still confirming identities accurately.
Now let’s look at the leading biometric modalities used for access control.
Types of Biometric Authentication Technologies

There are several distinct technologies available for biometric authentication. Each has its own mechanisms, accuracy levels, and ideal use cases.
Fingerprint Recognition

Fingerprint recognition analyzes the patterns, ridges, and minute features found on human fingertips. It focuses on identifying characteristics like arches, loops, whorls, and minutiae points.
A fingerprint scanner captures the user’s finger image, extracts key attributes, and matches them against enrolled templates.
Advantages
- Fast authentication requiring only a quick touch
- Provides medium to high accuracy
- Compact sensors, easy integration
- Proven technology with massive global usage
Thanks to its ubiquity and ease of use, fingerprint recognition is the most widely adopted biometric technology today. It is well-suited for most access control requirements.
Facial Recognition

Facial recognition analyzes the unique shape, contours, and proportions of an individual’s face. It measures nodal points between key facial features like eyes, nose, mouth, cheeks, chin, and forehead.
A camera captures the user’s facial image and extracts attributes for template creation. During authentication, the live face image is matched to enrolled templates.
Advantages
- Touchless authentication via standard cameras
- Can be integrated with CCTV surveillance systems
- Capable of one-to-many identification
- More hygienic compared to fingerprint readers
Facial recognition is being increasingly combined with fingerprints for enhanced security. It also enables touch-free access, which is vital during pandemics.
Iris Recognition

Iris recognition scans and analyzes the colored ring-shaped membrane surrounding the pupil of the eye. Irises contain a complex high-contrast pattern that is unique to each person.
An iris camera captures the image and creates templates for enrollment and matching.
Advantages
- Extremely accurate with negligible false acceptance rates
- Stable over a lifetime with no duplicates across humans
- Contactless authentication using specialized cameras
- Resilient against spoofing due to iris complexity
Iris scanning provides reliable authentication for high-security environments like government offices, nuclear facilities, and airports.
Voice Recognition

Voice recognition analyzes over 100 distinct characteristics of an individual’s voice for biometric identification. This includes tone, pitch, frequency, accent, cadence, pronunciation styles, and more.
A microphone records the user’s speech and creates voice prints for template creation and matching.
Advantages
- Completely hands-free and convenient
- Can be easily combined with speech recognition
- Enables continuous biometric monitoring and screening
Voice recognition provides secondary authentication and is useful for multi-factor access control.
Palm Print Recognition

Palm print recognition scans the palm using near-infrared light to capture the unique pattern of ridges, creases, and blood vessels present below the skin’s surface.
An infrared palm scanner is used to create enrollment and authentication templates.
Advantages
- High accuracy with low false acceptance and rejection rates
- Very difficult to counterfeit or alter
- More user-friendly compared to fingerprints
While less common than fingerprints and face recognition, palm biometrics also deliver reliable authentication for access control.
Behavioral Biometrics
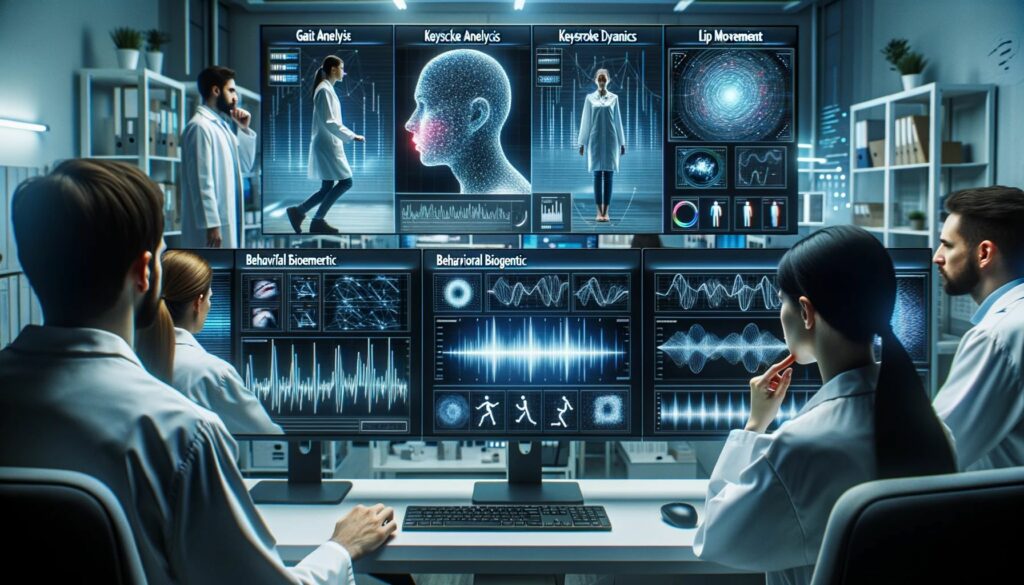
Behavioral biometrics like gait recognition, keystroke dynamics, and lip movements have niche applications mainly for continuous screening:
- Gait recognition – Analyzes body mechanics and walking style using floor sensors
- Keystroke dynamics – Recognizes typing rhythm patterns of individuals
- Lip dynamics – Examines lip movements and mouth shapes during speech
These can silently verify authorized users and detect imposters.
Multi-Modal Biometrics

Using a combination of fingerprint, face, iris, voice, and other biometrics enables robust multi-factor authentication. This offers an added layer of security for high-risk environments.
Multi-modal biometric systems fully utilize the strengths of each modality for unprecedented accuracy and security.
Now that we have explored the leading biometric technologies, let’s examine the concrete benefits they offer for access control.
The Benefits of Biometric Access Control

Biometric access control systems provide significant advantages compared to traditional mechanisms like keys, pin codes, and ID cards:
Enhanced Security
The most significant benefit biometrics offer is robust security. Human traits like fingerprints and irises are unique to each individual. Imposters can’t duplicate or share biometric credentials. Even identical twins have distinguishing attributes.
This ensures that only authorized staff can enter restricted areas. Multi-modal systems combining fingerprints, facial recognition, iris scans, and other biometrics take security to the next level. This protects access to sensitive facilities and data centers.
Greater Accuracy
Advanced biometric recognition algorithms can authenticate individuals with over 99% accuracy. Fingerprint scanners can differentiate between even identical twins based on minute fingerprint details. Such precision is impossible with ID cards or PINs.
Biometrics eliminates human errors in issuing and managing physical credentials that can lead to unauthorized access. Identity verification becomes quick and foolproof.
Superior Convenience
With biometrics, employees no longer need to carry ID cards or remember PIN codes to enter offices and restricted areas. A quick fingerprint or face scan provides easy, fast access.
Biometrics eliminates tedious access control processes. Employees get touchless entry within seconds without finding and presenting physical credentials. This improves workplace experience and productivity.
Detailed Audit Trails
Biometric systems log a detailed audit trail of all access transactions. Timestamps, user details, entry granted/denied status, and related metadata are recorded for each access attempt.
This enables compliance reporting, forensic analysis, and detection of unusual patterns. Security teams gain deep visibility into access activity.
Adaptability
Biometric systems easily accommodate company growth and changing access requirements. Adding a new user just requires their biometric enrollment. Access privileges can be quickly provisioned or revoked through software.
Legacy credential systems involve considerable time and costs for issuing cards or codes to new employees. Biometrics seamlessly scale with evolving security needs.
Cost Savings
The high upfront costs of biometric systems are offset by long-term operational savings. Once deployed, there are no recurring expenses for replacing cards, keys, or codes. Biometrics become increasingly affordable as sensor prices decline.
Regulatory Compliance
Biometric access control allows organizations to comply with stringent government and industry security regulations for access management. Examples include HIPAA, FISMA, PCI DSS, SOX, GLBA, and GDPR.
In summary, biometrics bring unmatched security, accuracy, adaptability, and convenience to access control systems. But to reap these benefits, they must be carefully implemented as discussed next.
Implementing Biometric Access Control Systems

Here are the key steps involved in deploying biometric authentication for access control:
Security Audit & Requirements Analysis
Conduct a comprehensive audit of current access control systems and processes. Identify vulnerabilities, gaps, risks, and compliance needs. Define security goals and assess how biometrics can help achieve them.
Analyze which areas, assets, data, and systems need biometric protection. Consider future scalability requirements as well. This helps select optimal biometric modalities.
Selecting Biometric Modalities
Choose the right biometric authentication technologies based on factors like:
- Security level required – Fingerprints, face, iris or multi-modal
- User convenience – Easy interaction, touchless options
- ROI – Upfront costs, maintenance needs, and lifespan
- Scalability – Accommodating increased users, locations, and integrations
- Usage conditions – Indoor/outdoor, lighting, environment
Integration with Existing Infrastructure
The new biometric access control system should integrate at both the software and hardware levels with existing systems:
- Physical access systems – Door locks, turnstiles, elevators
- Logical access systems – Directory services, SSO, IAM/PAM systems
- HR databases – For identity lifecycle management
- CCTV – For multi-factor facial recognition
This enables centralized orchestration and unified workflows. Open APIs help connect biometric endpoints with other security platforms.
Installing Biometric Readers
Certified biometric readers must be installed at all entry points like doors, turnstiles, elevators, stairs, server rooms, parking gates, and more. Positioning should balance security, user convenience, and connectivity.
User Enrollment & Training
Authorized users must be registered into the system by capturing their biometric data to create reference templates for authentication. Staff should be educated on properly interacting with biometric devices.
Testing & Certification
Conduct intensive testing to verify accuracy, reliability, and security before production deployment. Red team attacks help validate resilience to spoofing. Third-party certification provides added trust.
Monitoring, Maintenance & Updates
Closely monitor biometric systems using detailed access logs and reports. Continuously enroll new users, update firmware/software, and perform repairs and replacements to ensure optimal performance.
Data Protection & Privacy
Securely store biometric data using encryption. Limit database access to essential staff. Comply with data protection laws and conduct periodic audits to ensure security. Monitor systems for unauthorized activity.
With a phased approach and attention to the above aspects, organizations can realize the full potential of biometric access control. But adoption is just the first step – ongoing maintenance is equally critical for sustaining performance and security.
Transforming Workplace Security with Biometrics

Biometric access control systems greatly strengthen workplace security:
Stringent Access Restriction
- Allow entry to sensitive office areas only to specific employees based on their role
- Eliminate tailgating by verifying each individual trying to enter
- Continuously authenticate staff using CCTV cameras integrated with facial recognition
- Automatically lockdown facilities when threats are detected
Insider Threat Prevention
- Instantly revoke system access for terminated employees
- Closely monitor access by privileged users like system/security admins
- Get alerts on suspicious repeat access attempts or unusual timings
- Detect unauthorized access based on geolocation, time, and behavioral patterns
Enhanced User Convenience
- Employees can securely enter offices just using their fingerprint or face
- No more fumbling for access cards or remembering PINs
- Streamline office entry after lunch breaks and on weekends
- Touchless options like face recognition enhance pandemic safety
Biometrics make workplace access highly secure while also being frictionless for authorized staff.
Some leading examples of biometrics transforming workplace security:
- Government offices – Multiple biometrics safeguard sensitive departments and documents
- Data centers – Restrict access to server rooms using iris scanning
- R&D facilities – Leverage fingerprints and facial recognition to protect intellectual property
- Critical infrastructure – Limit access to control rooms managing utilities, telecom networks, etc. based on palm scans
- Law firms – Secure client files and financial documents via multi-modal biometric access
Biometric systems significantly bolster security while facilitating seamless access for employees. Adoption is picking up across sectors like technology, healthcare, finance, manufacturing, retail, and education.
Next, let’s look at how biometric technology itself will advance in the coming years.
The Evolution Roadmap for Biometric Access Control
Biometric authentication systems will continue progressing with technological improvements:
Expanding the Biometric Palette
- More biometric modalities will emerge, including vein recognition, DNA matching, microbiome profiling, ear shapes, and lip dynamics.
- This expands options for multi-modal systems to combine more human traits.
Integration with Cutting-Edge Technologies
- Biometrics will integrate more deeply with smartphones, edge computing, cloud platforms, IoT sensors, and video analytics.
- This enables centralized orchestration and automation of access control workflows.
Focus on User Experience
- Vendors are working on making biometric experiences seamless, hygienic, and fast.
- For example, contactless 3D facial recognition and on-device authentication will become more common.
Advanced Spoof Mitigation
- Algorithms will continue improving to detect even more sophisticated spoofing attempts using fakes, masks, and synthetic biometric replicas.
- Liveness detection will become highly robust.
Decentralized Authentication
- On-device biometric authentication using smartphones will reduce reliance on dedicated biometric hardware.
- For example, employees can enter offices by scanning their faces on their phones.
Improving Inclusivity
- Algorithms are being enhanced to work equally well across skin tones, ages, and disabilities like missing fingers.
- This makes biometrics more equitable and free from demographic bias.
Affordability and Mainstream Adoption
- As global adoption increases, biometric system costs will decrease through economies of scale.
- Ease of implementation and maintenance will improve via cloud delivery models.
Within this decade, biometric access control will likely become the predominant approach for robust physical access security across sectors.
Factors to Consider Before Adopting Biometrics

While promising, some key aspects of biometric systems should be analyzed before investment:
Cost of Implementation
The upfront costs of biometric software, hardware, integrations, installation, testing, and certifications can run into tens of thousands of dollars. Large systems easily cost over $100,000.
However, the ROI in terms of security and workplace efficiency outweighs the initial expenditures. Ongoing costs are relatively low.
Internal Skills Requirement
IT teams need adequate knowledge of biometric technology to handle integration, interoperability, database management, device maintenance, vendor management, vulnerability management, and related tasks.
Investment in technical training is crucial to ensure smooth operations and quick issue resolution. Consider getting professional services to supplement internal skills.
Change Management Requirements
The workforce must be educated on properly interacting with new biometric systems for accurate enrollment and authentication. Get employee feedback to assess usability.
Effective change management ensures user adoption across locations. Appoint power users as champions to drive adoption.
Reliance on Biometric Hardware Integrity
Fingerprint readers, facial recognition cameras and related hardware must always remain fully functional for business continuity. Their failure can bring access control to a halt.
So maintainable hardware with redundancy and failover capabilities is recommended. Keep spare parts to minimize downtimes.
Selection of Modalities and Vendors
Choosing biometric modalities and vendors based on factors like security needs, scalability, costs, uptime record, and long-term roadmap is key to success.
Partner with reliable vendors providing standards-based solutions. Ensure they have strong regional support capabilities.
Developing Fallback Procedures
Define procedures to securely handle exceptions like new users not yet enrolled, hardware failures, connectivity outages, software issues, and extreme biometric presentation difficulties.
Fallbacks help maintain productivity while keeping security intact.
Ensuring Compliance and Privacy
Organizations must comply with biometric data privacy laws like GDPR while securing personal information. Conduct recurring audits on biometric systems.
With careful planning, organizations can maximize returns on investment from biometric access control and sidestep pitfalls.
Conclusion

Biometric authentication delivers unmatched security, accuracy, adaptability, and convenience for physical access control systems. Biometrics verify identity based on unique human characteristics that are impossible to duplicate or share.
With continuous improvements in recognition algorithms, sensors, connectivity, and integrations, biometric access control is poised to supersede conventional mechanisms across industries. To fully benefit, organizations must evaluate internal skills, change management needs, and fallback procedures before adoption. But the ROI in terms of security and efficiency makes biometrics a wise long-term investment.
As biometric technology continues maturing, organizations worldwide are waking up to its potential. The unique human traits that power biometric systems provide the confidence to securely say yes to authorized users and no to everyone else trying to gain entry. Biometric access control is undoubtedly the way of the future.
Jefferson Security Systems is Here to Help

For organizations in the Philadelphia metro area, Jefferson Security Cameras offers professional biometric access control solutions tailored to your needs and infrastructure. Jefferson Security helps offices, healthcare facilities, schools, warehouses, and other businesses implement secure biometric systems.
Their experienced technicians handle the entire implementation – security audit, product selection, doors/hardware integration, user training, maintenance, and support. Ongoing services ensure your biometric access system keeps working optimally.
To learn more about deploying future-proof biometric access control for your organization, call Jefferson Security Cameras at (267) 662-1423 or request a quote today.
FAQs
What are the most common biometric modalities used for access control?
The most popular biometric modalities are fingerprint recognition, facial recognition, iris scanning, and voice recognition. Fingerprints are the most ubiquitous due to their low cost and ease of use. Facial recognition is also gaining traction due to touchless authentication benefits.
How accurate are biometric systems?
Leading biometric technologies like iris scanning, fingerprints, and palm recognition have accuracy rates of over 99% based on low false acceptance and false rejection rates. Multi-modal systems further boost accuracy. However, facial recognition accuracy can vary based on lighting conditions and the angle of subject capture.
What is liveness detection in biometrics?
Liveness detection refers to capabilities that enable biometric systems to determine if the biometric sample presented is an actual measurement from the authorized live person rather than a fake or spoof. This prevents attacks using replicas like silicone fingerprints.
Does weather impact biometric systems?
Environmental factors like sunlight, rain, snow, and dust can degrade the performance of some biometric devices. Fingerprint scanners may have trouble in very cold and dry weather due to lack of moisture. Facial recognition struggles in poor lighting. Choosing hardware rated for outdoor use is vital.
How are biometric templates stored securely?
Biometric templates contain highly sensitive information so they must be stored securely. Encryption protects the data, while irreversible cryptographic hashing converts templates into mathematical representations. Multi-factor access controls, activity monitoring, and key management help safeguard biometric databases.












